Digital payments are everywhere, but so are the risks lurking behind them. Fraud, data breaches, and system failures happen more often than most people realize.
At Web3 Enabler, we’ve seen firsthand how these vulnerabilities can derail businesses. This post breaks down the real threats you need to watch out for.
Where the Real Money Gets Stolen
Hackers stole $3–4 billion in crypto assets since 2017 according to UN monitors, with proceeds funnelled into funding operations. That’s not theoretical risk-that’s actual money vanishing from actual businesses. The problem isn’t that digital payments are inherently broken; it’s that most organizations treat security like a checkbox instead of a continuous battle. Fraud erupts when criminals exploit the gap between what you think is protected and what actually is. Unauthorized transactions occur because authentication systems have weak spots, employees click malicious links, or legacy systems were never designed to handle modern threats. The uncomfortable truth is that your biggest vulnerability isn’t the technology-it’s how you’re using it.
Outdated Encryption Leaves You Exposed
Many businesses still rely on outdated cryptographic algorithms like 3DES and SHA-1 to protect payment data, even though these have known vulnerabilities. If you store encrypted payment information for compliance reasons, understand that data retained for 7 to 10 years or longer becomes a target for future decryption attacks as computing power improves. Start by auditing which cryptographic algorithms actually protect your critical payment systems right now. Check your high-volume APIs, gateways, and authentication flows first-these are where attackers focus their energy. If you find RSA or ECC encryption protecting sensitive data, you need a timeline for upgrading to quantum-resistant alternatives before the threat becomes catastrophic.
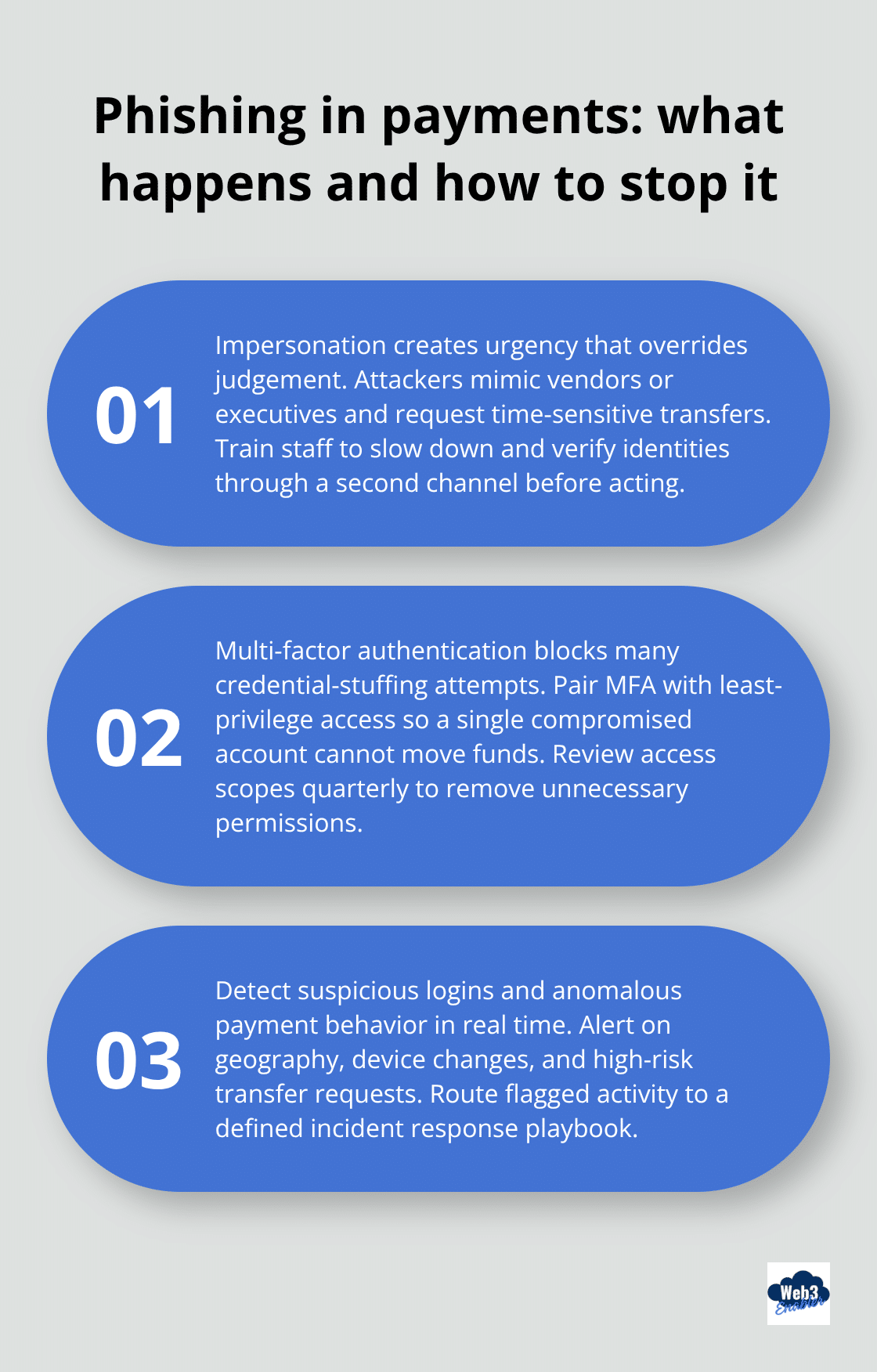
Phishing Still Works Because People Still Fall For It
Social engineering attacks succeed at scale because they exploit human behavior, not technical flaws. Criminals send messages that look legitimate, employees authenticate with stolen credentials, and suddenly attackers have access to your payment infrastructure. The 2025 threat landscape shows that even security-conscious teams get compromised when attackers impersonate trusted vendors or executives requesting urgent transfers. Your technical controls mean nothing if someone grants an attacker legitimate access. Train your team to verify requests through secondary channels, enforce multi-factor authentication on all payment-related accounts, and monitor for suspicious login patterns.
Building Layered Defenses That Actually Work
Implement layered security that combines strong encryption, robust governance, and incident response readiness. When you integrate third-party services-fintech providers, payment processors, wallet solutions-verify that their cryptographic practices are current. Weak security in an external API becomes your weak security. If you’re moving toward blockchain-based or stablecoin payments, demand that providers demonstrate how they protect transaction data and private keys. The vendors you choose matter as much as the controls you build internally.
Regulatory and Compliance Risks
The moment you move money across borders or accept payments from customers in different countries, you enter a regulatory minefield where the rules aren’t just different-they actively contradict each other. The European Union demands strict data residency and privacy controls under GDPR, while the United States treats financial data differently under PCI DSS and state-level regulations. Singapore’s Monetary Authority enforces different stablecoin rules than the Reserve Bank of India, which takes yet another stance. What’s compliant in one jurisdiction becomes illegal in another, and most payment systems weren’t designed to handle this complexity. Your team needs to map where your customers actually live, what payment methods they use, and which regulations apply to each transaction. This isn’t a one-time audit-regulatory environments shift constantly, and staying behind the curve costs money through fines, forced system overhauls, or worse.
KYC and AML Requirements Demand Real-Time Precision
Anti-money laundering and know-your-customer requirements exist for legitimate reasons, but they’ve become operationally exhausting. Financial institutions must verify customer identity, monitor transaction patterns for suspicious activity, and report anything flagged to authorities. The Financial Action Task Force sets global standards, but each country implements them differently. Over 94 billion dollars in stablecoin payments were settled between January 2023 and February 2025, and regulators are intensely focused on tracking those flows. Your payment infrastructure needs real-time monitoring systems that flag unusual patterns without creating false positives that paralyze legitimate business. If you’re moving toward stablecoin or blockchain-based payments, your provider must embed AML controls directly into the transaction flow, not bolt them on afterward. Weak compliance here triggers regulatory investigations that consume months of your team’s time and damage customer trust irreversibly.
Cross-Border Payments Require Operational Precision
Moving money internationally used to mean three-to-five day settlement windows and opaque fee structures. That’s changing, but the regulatory burden hasn’t lightened. Each country’s central bank, tax authority, and financial regulator wants visibility into cross-border flows. SWIFT remains the backbone of traditional international payments, but it’s slow and expensive. Stablecoins and blockchain-based solutions can settle cross-border transactions in minutes with transparent fees, yet regulators are still writing rules around them. If you operate in regulated industries like fintech, insurance, or lending, your cross-border payment strategy must include documentation that proves compliance with each jurisdiction’s regulations. Don’t assume that acceptance in one market means acceptance in another.
Compliance Automation Prevents Regulatory Gaps
The operational reality is that compliance automation matters more than ever-manual tracking creates gaps, and gaps create liability. Your team needs systems that connect payment flows to regulatory requirements without requiring spreadsheet management. When you integrate blockchain payments with your existing corporate infrastructure, you gain visibility into which transactions hit which regulatory requirements automatically. This approach eliminates the manual work that causes compliance failures and reduces the time your team spends on documentation. The vendors you choose for payment processing and blockchain integration should offer compliance visibility built into their core product, not as an afterthought.

As regulatory pressure intensifies and payment methods multiply, the next challenge emerges: your technical infrastructure must keep pace with both compliance demands and security threats simultaneously.
Operational and Technical Risks
Your payment infrastructure exists in constant tension between legacy systems that were never designed for real-time transactions and modern requirements that demand uptime measured in nines rather than percentages. System downtime in payment processing isn’t a minor inconvenience-it’s a revenue killer. When your payment gateway fails for even 15 minutes during peak business hours, you lose transactions and damage customer trust that takes months to rebuild. Most businesses run payment systems across multiple platforms: older on-premise infrastructure handling core processing, cloud-based gateways handling customer-facing transactions, and third-party integrations connecting everything together. Each connection point represents a failure risk. Your legacy ERP system might process invoices every four hours in batch mode, while your new stablecoin payment provider settles transactions in real-time. That mismatch creates reconciliation nightmares and exposes you to fraud because your accounting systems can’t keep pace with actual fund movement. Integration issues don’t announce themselves-they hide in edge cases until a high-value transaction fails and your team scrambles to figure out why your systems disagree about what actually happened.
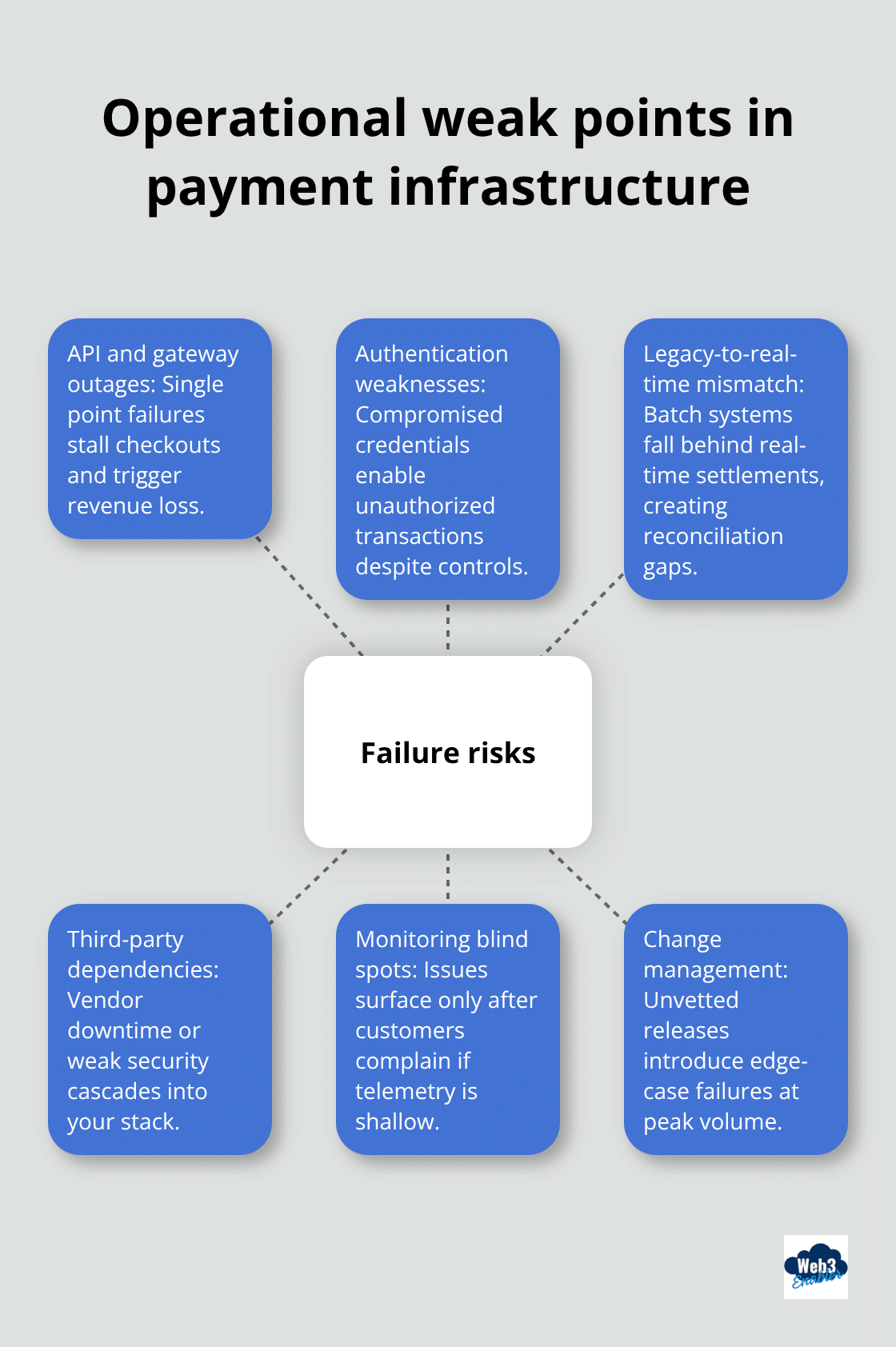
Map Your Highest-Risk Payment Flows
The practical fix starts with infrastructure assessment and honest prioritization. Identify which systems handle your highest-volume payment flows and which ones would cause the most damage if they failed. Your APIs, gateways, and authentication systems deserve redundancy and failover capability because they’re where attackers focus their energy and where downtime costs multiply fastest. Implement real-time monitoring that alerts your team the moment transaction volumes drop or settlement times spike, not after customers complain. When you evaluate blockchain-based or stablecoin payment solutions, ask providers to show you their uptime track record and how they integrate with your existing accounting software. Your provider’s infrastructure directly impacts your operational stability.
Eliminate Reconciliation Lag
Move beyond manual reconciliation by upgrading to systems that support real-time settlement and instant reconciliation-this eliminates the lag where transactions exist in payment limbo while your books show something different. Vendors offering API-first infrastructure and transparent settlement processes reduce integration friction significantly. The gap between when money actually moves and when your systems reflect that movement creates operational blind spots that expose you to fraud and accounting errors. Real-time reconciliation keeps your financial records accurate and your team informed about actual cash position.
Test Before You Deploy at Scale
Test new payment methods with trusted partners before rolling them out broadly, giving your team time to identify integration problems without jeopardizing customer transactions. This approach catches edge cases that your internal testing missed and builds confidence in new payment channels before they touch production traffic. Your team learns how the new system behaves under real conditions, and your partners benefit from early access to capabilities they might want to adopt. As you layer in new payment capabilities, your security posture must strengthen simultaneously because more payment channels and integrations mean more attack surfaces for attackers to exploit.
Final Thoughts
The risks in digital payments stem from treating security and compliance as static rather than continuous operations. Fraud, data breaches, regulatory violations, and system failures all accelerate when your team stops monitoring, your cryptographic protections age, and your compliance systems fail to adapt to shifting regulations. You need real-time visibility into transaction flows, current cryptographic protections, and compliance infrastructure that evolves as rules change-and you need all three working together simultaneously.
Your path forward requires three concrete actions. First, audit your payment infrastructure honestly and identify which systems pose the highest risk if they fail or get compromised. Second, upgrade your cryptographic protections and implement real-time monitoring that catches problems before they become disasters. Third, test new payment methods with trusted partners before deploying them at scale, giving your team time to catch integration issues without jeopardizing customer transactions.
We at Web3 Enabler help businesses connect blockchain technology with their existing corporate infrastructure, making it possible to accept stablecoin payments and send global payments faster while maintaining the security and compliance controls your business requires. Explore how Web3 Enabler can strengthen your payment infrastructure and move beyond the risks in digital payments that traditional systems create.
Risks in Digital Payments FAQ
What are the biggest risks in digital payments for businesses?
The biggest risks in digital payments typically fall into four buckets, fraud and account takeover, data breaches, regulatory noncompliance, and operational failures like outages or reconciliation gaps. These risks grow as you add more payment methods, more countries, and more third-party integrations. The safest approach is treating payments as a constantly monitored system, not a one-time setup.
How does real-time payments increase fraud risk?
Real-time payments reduce the “reaction window” you used to have with slower settlement. Once funds move instantly, mistakes and fraud can become final before teams can intervene. To manage this, add stronger authentication, real-time risk scoring, velocity limits, and step-up verification for higher-risk transactions.
What causes most payment security incidents today?
Many payment incidents start with credential theft, phishing, vendor impersonation, or weak access controls, not a “hack” of the payment network itself. Once attackers get valid logins, they can initiate unauthorized payouts or change settlement details. Multi-factor authentication, least-privilege access, and payment approval workflows are core controls, not optional add-ons.
Why are outdated encryption algorithms a risk in payment systems?
Older cryptographic choices can weaken the security of stored or transmitted payment data over time. If your environment still relies on legacy algorithms or outdated implementations, you may be exposed to known weaknesses and compliance problems. Start with a cryptography audit across payment gateways, APIs, and tokenization or vault systems, then prioritize upgrades where sensitive data is stored, processed, or transmitted.
Does PCI DSS apply to my business if I accept card payments?
Yes, PCI DSS applies to organizations that store, process, or transmit cardholder data, and also to entities that can impact the security of the cardholder data environment. The fastest way to reduce scope is to avoid touching raw card data directly by using hosted payment pages, tokenization, and validated service providers. Your goal is minimizing where card data can live, and proving you can monitor and control access.
What are the biggest compliance risks for cross-border digital payments?
Cross-border payments create overlapping obligations, privacy rules, sanctions screening expectations, and recordkeeping requirements can differ by country. The risk is not just fines, it is forced changes, frozen funds, or losing payment partners when controls are weak. The practical fix is mapping customer locations, payment flows, data residency or transfer rules, and building automated compliance checks into the transaction lifecycle.
How does GDPR affect digital payments and customer data transfers?
If you process personal data tied to EU individuals, GDPR obligations can apply, especially around data minimization, security, and lawful processing. International transfers of personal data require specific safeguards or legal mechanisms, and you should confirm where your payment providers store and route data. Align contracts, vendor assessments, and technical controls so cross-border processing does not become an after-the-fact scramble.
What is the FATF Travel Rule and why does it matter for crypto or stablecoin payments?
The FATF “Travel Rule” refers to standards that require certain originator and beneficiary information to travel with payments, and it is especially relevant for virtual asset transfers handled by regulated providers. If you accept stablecoins or route payments through virtual asset service providers, your processor should handle Travel Rule data exchange and screening automatically. If they cannot, you risk delays, rejections, or compliance exposure in jurisdictions that enforce these requirements.
How do operational and technical failures show up in digital payment systems?
Common operational risks include gateway downtime, processor outages, mismatched settlement timing between systems, broken webhooks, and manual reconciliation lag that hides errors. These issues can quietly leak revenue through failed payments, duplicate payouts, and customer churn. Mitigate this with redundancy, monitoring for declines and latency spikes, clear incident response playbooks, and automated reconciliation tied to your ERP or accounting system.
What is the safest way to test new payment methods before scaling?
Run a controlled pilot with real transactions, clear success metrics, and strict limits on exposure. Track authorization rates, fraud and chargebacks, settlement time, reconciliation accuracy, and support tickets, then compare against your baseline. Only scale after the pilot proves stability, compliance fit, and measurable ROI in your environment.